CyberVaR 360™
Cyber Risk in Dollars, Not Colors

Ready to Turn Your Cyber Signals into Clear Action?
CyberVaR 360™ delivers executive-ready cyber briefings tailored to your environment so your team knows what to patch first, what active threats matter now, and what to prioritize next.
Two Briefings. Two Different Decisions.
Executive Cyber Exploit Brief
Twice-weekly “fix first” brief built from CISA KEV and FIRST EPSS.
Active Threat Exposure Brief
Monthly threat brief built from current CISA advisories, ransomware alerts, and malware analysis reports.
Latest Articles
-
SharePoint’s Quiet RCE: Why CVE-2026-20963 Demands Immediate CISO Attention
CISA now says CVE-2026-20963 is being actively exploited. Microsoft patched it in January. The real issue is not just the score. It is what this flaw says about patch latency, SharePoint exposure, and executive accountability.
-

Executive Cyber Exploit Brief — March 20, 2026
This is a 2-minute exploit brief for executives: what changed, who is exposed, and what to do in the next 72 hours.
-

Executive Cyber Exploit Brief — March 13, 2026
This is a 2-minute exploit brief for executives: what changed, who is exposed, and what to do in the next 72 hours.
-

Executive Cyber Exploit Brief — March 11, 2026
This is a 2-minute exploit brief for executives: what changed, who is exposed, and what to do in the next 72 hours.
-

Executive Cyber Exploit Brief — March 09, 2026
This is a 2-minute exploit brief for executives: what changed, who is exposed, and what to do in the next 72 hours.
-

Executive Cyber Exploit Brief (for last 7 days) — March 05, 2026
This is a 2-minute exploit brief for executives: what changed, who is exposed, and what to do in the next 72 hours.
-

The Business Case for Cyber Value at Risk (VaR) – Translating Threats into Dollars
Cyber Value at Risk (Cyber VaR) translates vague threat discussions into clear financial terms. Instead of relying on heatmaps or qualitative scores, executives can see their likely, average, and worst-case cyber losses—expressed in dollars. By applying proven financial risk methods like Monte Carlo simulation, Cyber VaR gives leaders visibility into tail risks, insurance gaps, and…
-

From Risk Matrices to Dollar-Based Insight: Why Business Leaders Must Quantify Cyber Risk
From heatmaps to finance: use loss-exceedance curves to buy down tail risk and brief the board in dollars, not colors.
-

5 Key Reasons Your Organization Should Implement NIST CSF 2.0 Profiles
In today’s financial and banking sectors, effective cybersecurity is critical to safeguarding sensitive data, maintaining trust, and ensuring compliance with regulatory standards. As cyber threats continue to evolve, business leaders must not only protect their organizations but also align cybersecurity efforts with broader business objectives. The NIST Cybersecurity Framework (CSF) 2.0 offers a robust approach…
-

Python for Newbs – A Learning Path to Begin Programming in Python
Python is a powerful, versatile, and easy-to-learn programming language that has gained immense popularity among developers, data scientists, and businesses alike. Known for its clean and readable syntax, Python is designed to be beginner-friendly while also being robust enough for advanced applications.
-

A Simple Fix for This Common Anaconda Problem
If you run a “conda list” command from your terminal or command window on your Mac or Windows PC and see an error that looks like the one shown below, there is a simple fix.
-

Step-by-Step Guide: Installing Anaconda on Mac and Windows and Writing a Simple “Hello Py” Project in Jupyter Notebook
In this article, I will walk you through the process of installing Anaconda on both Mac and Windows, setting up your environment, and writing a simple “Hello Py” project in a Jupyter Notebook.
-

Cybersecurity Threats vs. Risks: What’s the Difference and Why It Matters
The concepts of “threats” and “risks” are fundamental to cybersecurity and are defined by both NIST (National Institute of Standards and Technology) and ISO/IEC (International Organization for Standardization/International Electrotechnical Commission) in slightly different but complementary ways.
-

AI-Driven Cyber Risk Management: Leveraging Bayesian Networks in Cybersecurity for Business Leaders
In the rapidly evolving landscape of cybersecurity, businesses face increasingly complex and dynamic threats. The traditional methods of risk management and decision-making are being challenged by the need for more adaptive, intelligent, and data-driven approaches. Enter Bayesian Networks, a powerful form of Artificial Intelligence (AI) that can significantly enhance your organization’s ability to identify, assess,…
-

NIST CSF 2.0 Pre-Assessment Checklist
In the modern digital landscape, cybersecurity has become a cornerstone of risk management for organizations across all industries. As cyber threats evolve, so must the frameworks and strategies organizations use to protect their assets.
-

Cybersecurity as a Boardroom Priority: Engaging the C-Suite in Risk Management with NIST CSF
In today’s rapidly evolving digital landscape, cybersecurity is no longer just a technical issue relegated to IT departments—it’s a critical component of business strategy that requires the attention and engagement of the entire C-suite and board of directors.
-
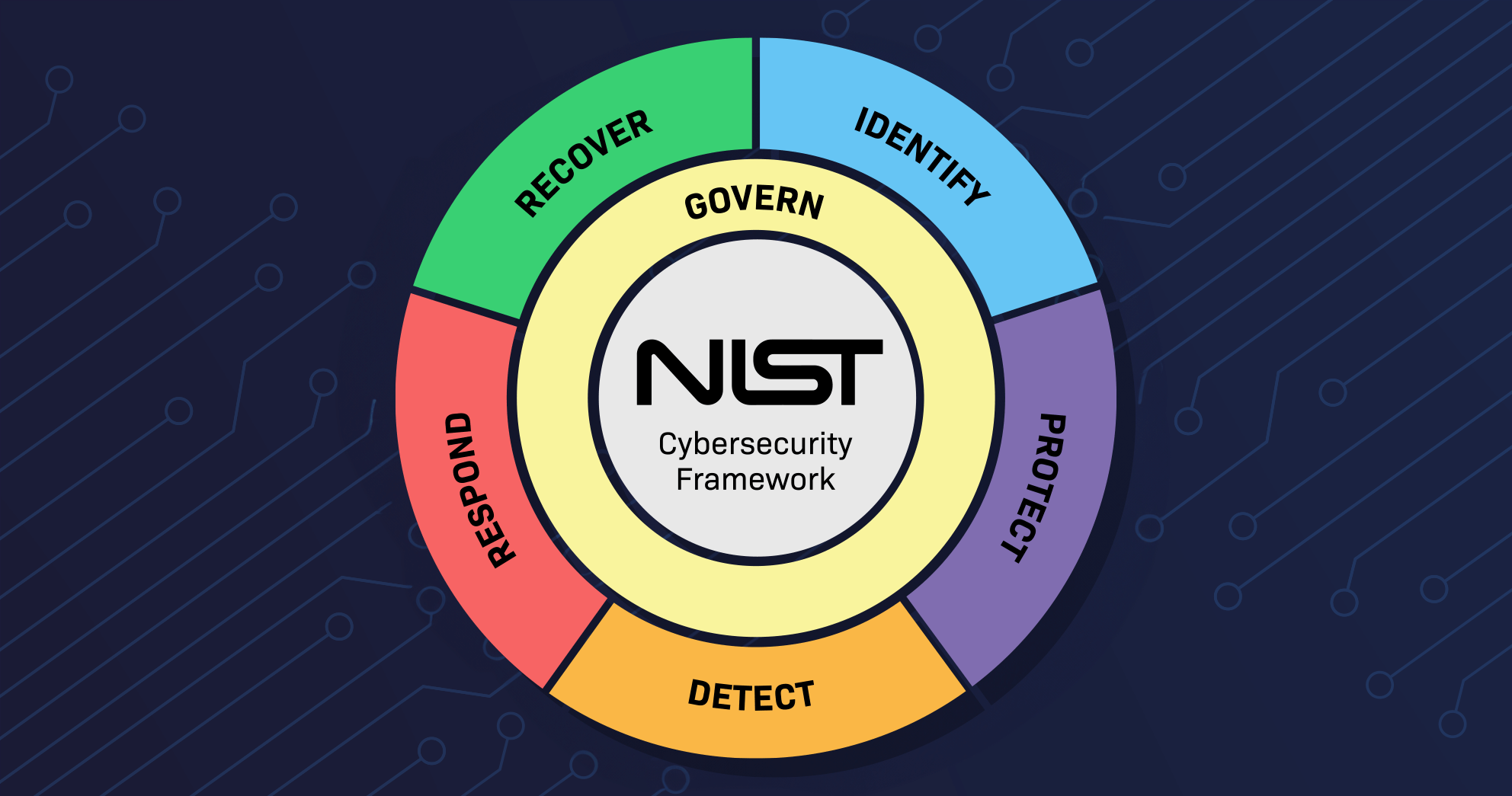
A Step-by-Step Guide to Implementing Organizational Profiles in NIST CSF 2.0
The NIST Cybersecurity Framework (CSF) 2.0 introduces several enhancements to help organizations manage their cybersecurity risks better. One of the most significant updates is the refined approach to Organizational Profiles. These Profiles are essential for understanding an organization’s cybersecurity posture, setting target objectives, and tracking progress over time. This step-by-step guide will walk you through…
-

Understanding and Communicating Cybersecurity Posture: The Value of NIST CSF 2.0
For senior business leaders, grasping the intricacies of cybersecurity might seem daunting, yet it is increasingly vital in today’s digital landscape. The NIST Cybersecurity Framework (CSF), now updated to version 2.0, offers a robust and flexible tool for understanding and communicating your organization’s cybersecurity posture. This framework is not just a technical resource; it is…
-

The Evolution of Cyber Risk Analysis: From The Risk Matrix to Bayesian Statistics
In the rapidly changing world of cybersecurity, the methods we use to assess and manage risk must evolve to keep pace with emerging threats. Traditional risk analysis methods, such as the risk matrix, have long been staples in the cybersecurity toolkit. However, as the complexity of cyber threats grows, these methods can fall short, offering…
-

Real-World Applications of Bayes’ Theorem in Cybersecurity
As the field of cybersecurity continues to grow in complexity, professionals are seeking more sophisticated methods to predict, prevent, and respond to cyber threats. Among the various tools at their disposal, Bayes’ Theorem stands out as a particularly powerful and versatile approach.
-

Why Bayes’ Theorem is a Game-Changer for Cybersecurity Risk Analysis
In the ever-evolving landscape of cybersecurity, where new threats emerge daily, and the stakes are higher than ever, organizations need more than just reactive strategies to protect their assets. They need a robust, data-driven approach to anticipate and mitigate risks before they manifest into serious breaches. This is where Bayes’ Theorem comes into play—a powerful…
-

Machine Learning vs. Bayesian Statistics in Python for Cybersecurity Risk Analysis
In this article, I explore the advantages and applications of two powerful analytical approaches: Machine Learning (ML) and Bayesian statistics in Python. Both methodologies have their unique strengths and are suited to different types of problems.
-

Estimating Phishing Email Frequency with the Poisson Distribution in Python: A Practical Guide for Cybersecurity Risk Assessment
In today’s article, I will show you how to use the Poisson distribution to estimate the number of phishing emails your organization receives per day. Understanding the frequency of these phishing attempts can help you adjust your incident response planning measures accordingly.
-
Analyzing Cybersecurity Risks: Estimating Phishing Attack Probabilities with Bayesian Statistics in Python Using Beta Distribution
In today’s digital landscape, cybersecurity threats are a significant concern for businesses of all sizes. Phishing attacks, where malicious actors attempt to deceive employees into revealing sensitive information or clicking on harmful links, are particularly prevalent.